Are you considering bypassing the firewall of your school, college, university, or workplace? Very well, then you’re at the right place. Here, you’ll find all the tips and techniques on how to skirt around firewalls and access the web without restrictions and censorship.
Also, you’ll find some details as to whether or not the entire process is legal or not. In addition, we’ve also shared some details on the advantages and disadvantages associated with bypassing firewalls. Read on for the details.
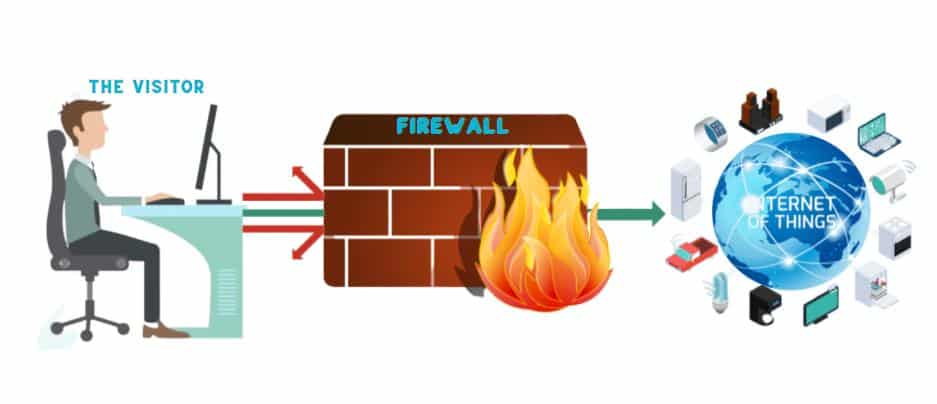
The process of circumventing firewalls largely depends on understanding their working mechanism. The principle of action for all firewalls is the same. However, their mechanisms of action are different. Meaning, while some firewalls monitor the characters you input in the address bar, others simply track the site’s traffic. In doing so, firewalls succeed in restricting access to particular web content. This protects the entire network against viruses, hackers, and other unauthorized third parties.
That being said, there are methods and techniques for bypassing firewalls. That’s partly what we’ll discuss in this article. So without wasting any more time, let’s get straight to the methods:
Using Software
If you want to bypass a firewall without leaving a trail, Tor browser is the way to go. The browser has a reputation for high-end anonymity and privacy. Tor is basically a browser that allows you to access restricted content anonymously. Despite the high-level privacy, security, and anonymity guarantee, Tor browser is at times painfully slow.
You might have to wait for much longer to access webpages you would otherwise access in split seconds. If you value speedy connections, then you may not like Tor quite much. In spite of that obvious downside, Tor is still loved by many users worldwide, especially people who’d want to keep their browsing activity private and anonymous.
The platform is compatible with android, macOS, Windows, and iOS. Also, it is accessible via all the top browsers like Firefox, safari, chrome, and Microsoft Edge. That means you can access and use Tor Browser on just about any device. It’s also noteworthy that the platform required no installation of software. As such, you won’t have to worry about Tor files and folders being installed on your device.
Using tor is as simple as it gets. All you do is visit the Tor browser site then start surfing as you’d do with any other browser. You’ll notice the slow loading speeds, but again that’s only expected with Tor. Just be happy that no one can ever catch a glimpse or trail of your online activities. That’s why we love Tor.
Pros
- High-level anonymity and privacy
- Best for bypassing all internet access restrictions
- Available on: windows, mac, android, iOS
- Encrypts all user data.
Cons
- Slow connection speeds
UltraSurf is one of the best software for bypassing not only firewalls but also internet access censorship. It’s powered by an HTTP proxy server and also features a data encryption protocol for enhanced online safety. UltraSurf is open-source software that was created to help users bypass access restrictions by governments. That said, the tool is very good for bypassing firewalls.
Unlike most tools for bypassing firewalls, this tool is free to download and does not install any files on your computer. The tool comes with optional browser extensions for Chrome and Firefox. That makes for quick and easy activation and use on the go. Note however that even without the chrome and Firefox extensions, you can still access UltraSurf using other popular browsers.
Currently, UltraSurf is only available on the Windows operating system. That might seem like a downside, especially for users who may prefer alternative operating systems.
Pros
- Combines anonymity and high-grade privacy features
- Supports user data encryption
- Supports HTTP proxy and encryption protocol
- Available chrome and Firefox extensions
- Open-source software
Cons
- Only available on the Windows operating system.
Using Connected Devices
1Using a Proxy
Using a Proxy
Web proxies are very popular when it comes to overriding internet access restrictions. They work by routing user traffic via alternative servers making it hard for firewalls to detect your online activity. For instance, if your school or company uses a firewall to restrict access to social sites, it is possible to use a proxy to visit such websites. It does this by concealing your actual traffic via an alternative IP address. Other reasons people use proxies include visiting gaming and streaming sites, downloading torrents, etc.
Web proxies for bypassing firewalls come in two distinct types; premium and free proxies. You can be sure the premium versions are far better than free proxies. In fact, free proxies usually come with many disadvantages in addition to their unreliability. So, unless you are an absolute beginner just starting out with proxies, it’s always recommended to use premium proxies for superior performance.
Most web proxies are available on almost all types of browsers. That means you can access them using just about any popular browsing tools such as Microsoft Edge, Firefox, chrome, safari, etc. It’s also worth noting that most proxy service providers are also compatible with android, windows, macOS, and iOS. Meaning you can use them on most common devices.
Remember there are many proxy service providers on the web. Therefore, it’s imperative that you compare the deliverable from different providers in order to get what’s best for you.
Next time you want to access your popular social sites, stream or download content over a firewall-protected network, try web proxies.
Pros
- Unrestricted surfing experience
- Saves bandwidth by caching files
- Available in free or premium plans
- Some may offer data encryption
- Available on android, mac, windows, iOS, etc.
Cons
- Free plans have slow connection speeds
- Possible personal data leaks
Read more,
2Using a VPN
Using a VPN

Even though VPNs and proxies can both be used to bypass firewall restrictions, the two are very different and distinct. The main differences lie in their mechanism of action, anonymity, and privacy features. While web proxies simply route your connection via an alternative network, VPNs encrypt your traffic besides routing via an alternative path. The data encryption function makes for better protection of user data in addition to bypassing firewalls.
That’s one reason VPNs are preferred over proxies. Note however that some proxy service providers have also included data encryption as part of their premium packages. Another reason VPNs are preferred over web proxies is their high-level anonymity and privacy. That simply means VPNs protect your user data from unauthorized access.
Also, most top VPN providers have a no history tracking policy. Meaning, they do not record or track your surfing activity, hence won’t sell your personal data to third parties. VPNs are also compatible with most operating systems such as windows, android, iOS, macOS, etc. Also, noteworthy is that most VPNs can be accessed using almost all popular browsers.
Some even have dedicated browser extensions for Chrome and Firefox. That makes for easy activation and use on the go. Bypassing firewalls doesn’t get any easier.
If you’re looking for a tool for bypassing firewall access restrictions without skimping on your privacy, VPN is worth giving a try.
Pros
- Privacy and anonymity guaranteed
- Best for bypassing firewalls and other access restrictions.
- Available in free and premium plans.
- Lightning-fast connection speeds.
- Supports personal data encryption
Cons
- None
Here is the top 5 VPN we have tested and recommended. Check it!
Using Smart Communication Tools

If you don’t want to deal with the hassle of using a proxy server, VPN, or Tor browser, then you can just simplify things by using your smartphone hotspot. Yes, you heard that right- use your smartphone as a hotspot. Here’s how it works.
First, ensure you’re subscribed to a data package. That will depend on your internet service provider and the plans available.
Next, turn on the device’s data and then switch on the hotspot. If you’ve ever had a smartphone before, then you must be familiar with its data and hotspot settings. With the phone’s hotspot on, go ahead and turn on your laptop’s Wi-Fi then connect to the internet. You can now access all your favorite sites without having to worry about the school’s or company’s firewall.
By using a smartphone’s hotspot to access the web, you may have to incur extra costs depending on your select data plan. Again that depends on your ISP.
Something else to note is that you won’t have to use the third-party software, like is the case with VPNs, proxies, or Tor. That’s important because you won’t have to worry about extra costs due to premium package subscriptions. Also, the browsing speed is top-notch; it depends upon your ISP’s network strength.
Lastly, by using a mobile hotspot, you get to bypass the school’s or company’s firewall without exposing the entire network to security vulnerabilities. That’s all. Next time you want to access your favorite sites over a firewall restricted network, consider using your smartphone’s hotspot. It’s simple yet very effective.
Pros
- The simplest way to bypass firewall
- No software installations required
- Instant access to your favorite gaming, streaming, or torrent download sites.
- No extra costs from premium package subscriptions.
- Fast connection speeds
Cons
- You may have to incur additional data charges
The Possible Consequences of Bypassing Firewall

The decision whether or not to bypass the firewall at your workplace or school depends on personal reasons. If you really need to access some restricted content online over a firewall restricted network, then you may have to bypass it. However, if there’s no real urgency in accessing particular sites over your school’s or company’s firewall restricted network, then you can as well not bother bypassing the restriction.
Remember that school or workplace firewalls are not only meant to protect the organization against online threats such as data breaches and virus attacks. At the workplace or school, firewalls are installed to promote productivity and learning besides preventing data breaches. As above mentioned, bypassing the firewall has its advantages and disadvantages. Among the advantages include the freedom to access just about any other website. The disadvantages are plentiful. Some of them include:
- Theft of sensitive company data.
Breaching the organization’s firewall might come with the risk of data leakage. That would mean sensitive info belonging to the organization of individuals being accessible to fraudsters. Moreover, bypassing the firewall might expose your device to harmful viruses that could potentially lead to irreparable damage.
- Expulsion or suspension from school.
In the case of bypassing the firewall of a learning institution, there’s the risk of expulsion or suspension. So, if you’re a student in a particular institution of learning, tread carefully before you decide to override the school’s firewall.
- Legal ramifications
Because of the risk of loss of personal data, institutions might choose to pursue a legal action that may lead to the incarceration and charging of the suspect. You may end up behind bars for a long time. You really need to give your actions serious thoughts before choosing to bypass an organization's firewall.
That being said, the decision to bypass a firewall should be well informed by the above-mentioned pros and cons.
FAQs
1. Is it safe to bypass firewalls?
Both yes and no. Yes in the sense that you will get access to restricted content like gaming, streaming, or torrent downloading sites. No, because it makes the school or workplace’s network vulnerable to data breaches, virus attacks, among other network-related concerns. Therefore, the decision pertaining to the safety of bypassing a network’s firewall should be informed by necessity after weighing between the associated pros and cons. It’s a choice for you to make.
2. Is firewall bypassing legal?
It’s both legal and illegal. It all depends on the type of content you access. Schools and organizations use firewalls to prevent unauthorized persons from accessing sensitive company information or personal data. In that respect, if you bypass the firewall and access such restricted content, you could be liable for legal prosecution. In that light, bypassing the firewall is considered illegal.
On the other hand, bypassing the organization’s firewall can be considered legal if it doesn’t pose any threat to the network’s integrity and the organization’s security. This might be the case if you bypass the company’s firewall using your smartphone’s hotspot and accessing the internet using a different device; not the institution’s computers.
3. What happens if the firewall is disabled?
Firewalls are meant to protect organizations against online threats due to unauthorized access and virus attacks. As such, disabling it would mean exposing the organization to the aforementioned threats. You could lose sensitive info due to system breaches by hackers and fraudsters. So, unless recommended by an expert, disabling an organization’s firewall isn’t advisable.
Conclusion
There are different ways for bypassing firewalls. They include the use of web proxies, VPNs, use of smartphone hotspot, or using tools such as UltraSurf and Tor Browser. Also, there are many reasons why people choose to bypass firewalls. Some of these include the need to download torrents, the desire to access restricted streaming or gaming sites, and to visit social sites.
It’s also worth noting that bypassing firewalls is completely legal if doing so doesn’t expose the network to potential threats.
However, it’s illegal to access restricted company info such as sensitive personal information. Remember, bypassing a firewall comes with both advantages and disadvantages. You may want to compare the pros versus cons before you decide whether or not to bypass an organization’s firewall.